Cybersecurity method learns from hackers by tricking them
Por um escritor misterioso
Descrição

White Hat Hacker - Roles and Responsibilities

How Hackers Use AI and Machine Learning to Target Enterprises - DT

Types of Cyber Security Threats

9 Examples of Social Engineering Attacks
Do you know if you were hacked? Do you know if some personal information was stolen from your system or account? Have you always wanted to learn how
Ethical Hacking : 3 in 1- A Comprehensive Beginner's Guide + Complete Tips And Tricks To Ethical Hacking + Learn Penetration Testing, Cybersecurity

What is Web Application Hacking? Methodology & Tutorial

Cyber Security Vulnerabilities Your Business Should Be Aware Of - Stanfield IT

What is Cybersecurity An Introduction to Cyber Security

List of Cybersecurity Software Tools To use in 2023
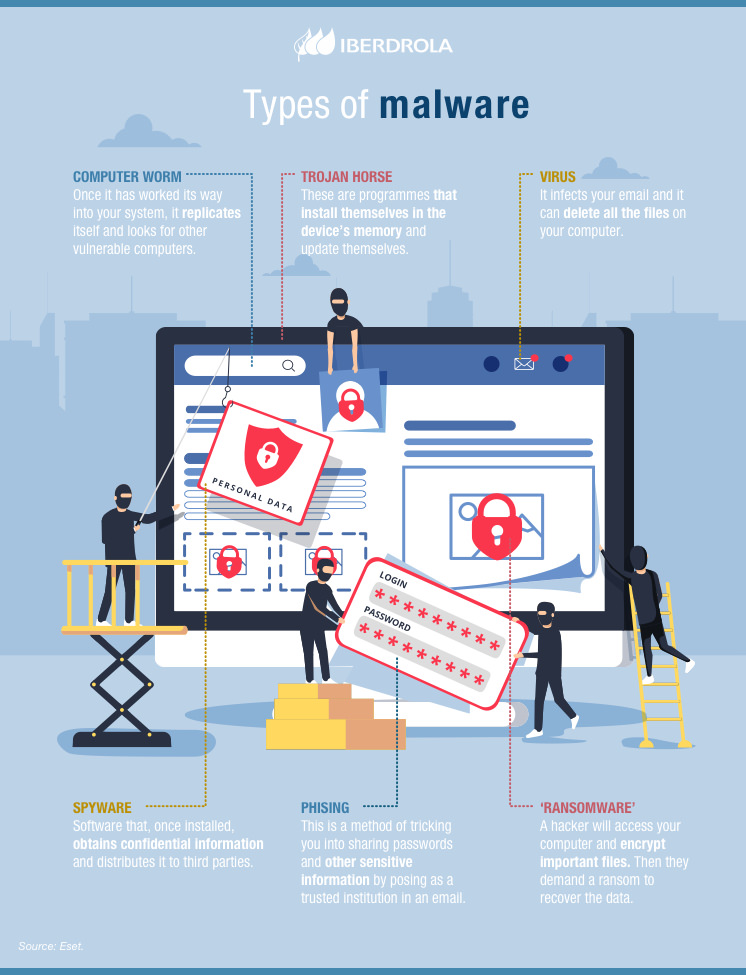
Ethical hacking, the best prevention for Cybersecurity - Iberdrola

The New Risks ChatGPT Poses to Cybersecurity

How AI and ML are Used in Cybersecurity? - InfosecTrain

15 Types of Hackers You Should Know About In 2023

Ethical hacking: attacking to improve
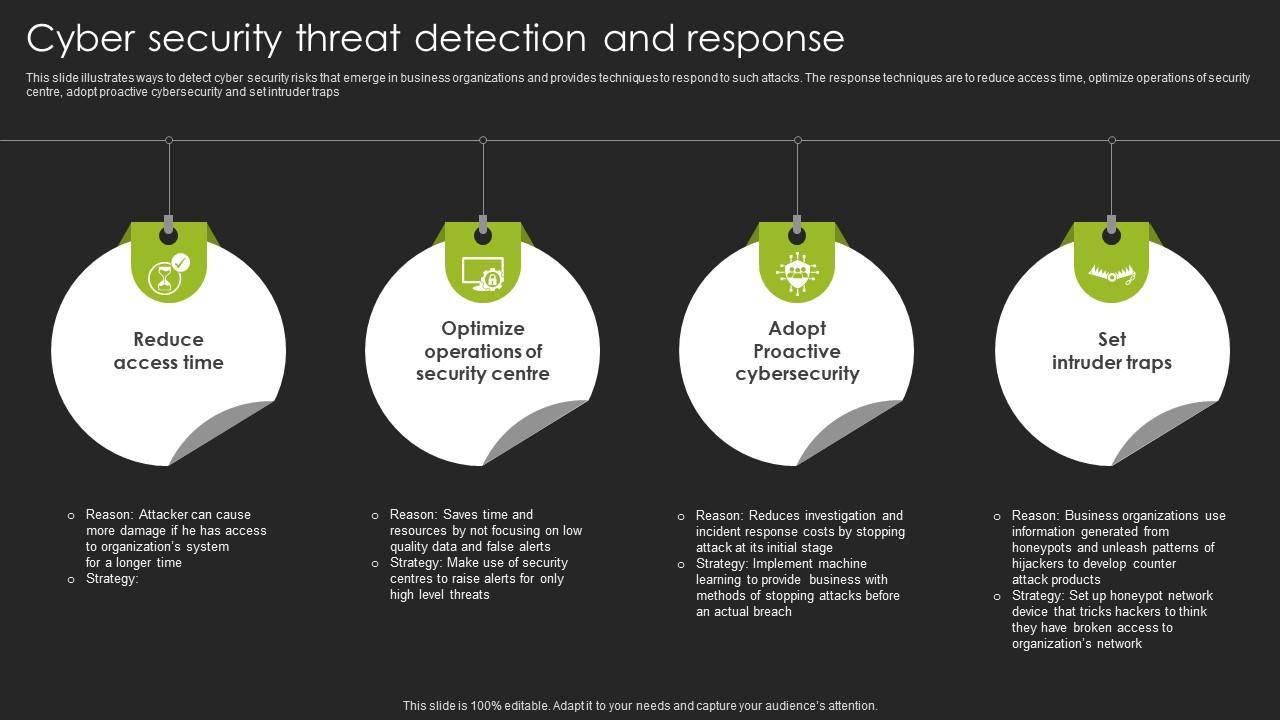
Cyber Security Threat Detection And Response
de
por adulto (o preço varia de acordo com o tamanho do grupo)