Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's
Por um escritor misterioso
Descrição
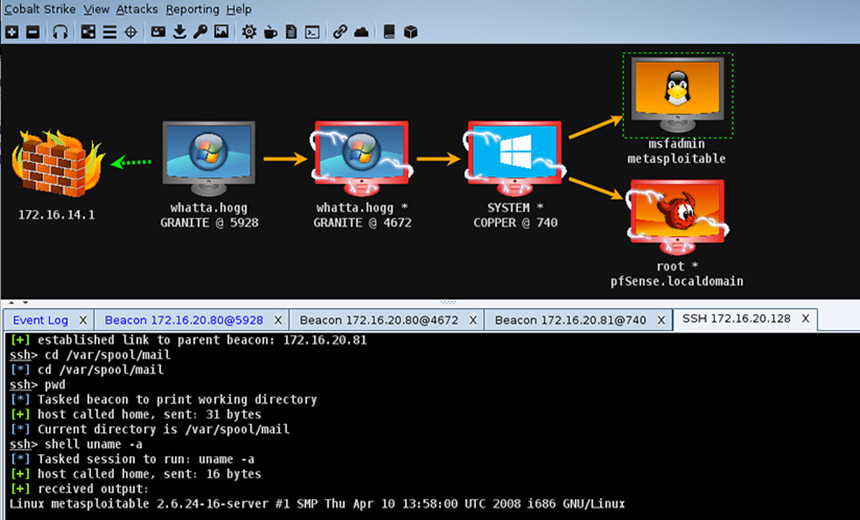
We analyzed tactics, techniques, and procedures utilized by threat actors of the FireEye’s stolen Red Team Tools. Attackers heavily used various defense evasion techniques.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
Ransomware: Beware of 13 Tactics, Tools and Procedures
Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's
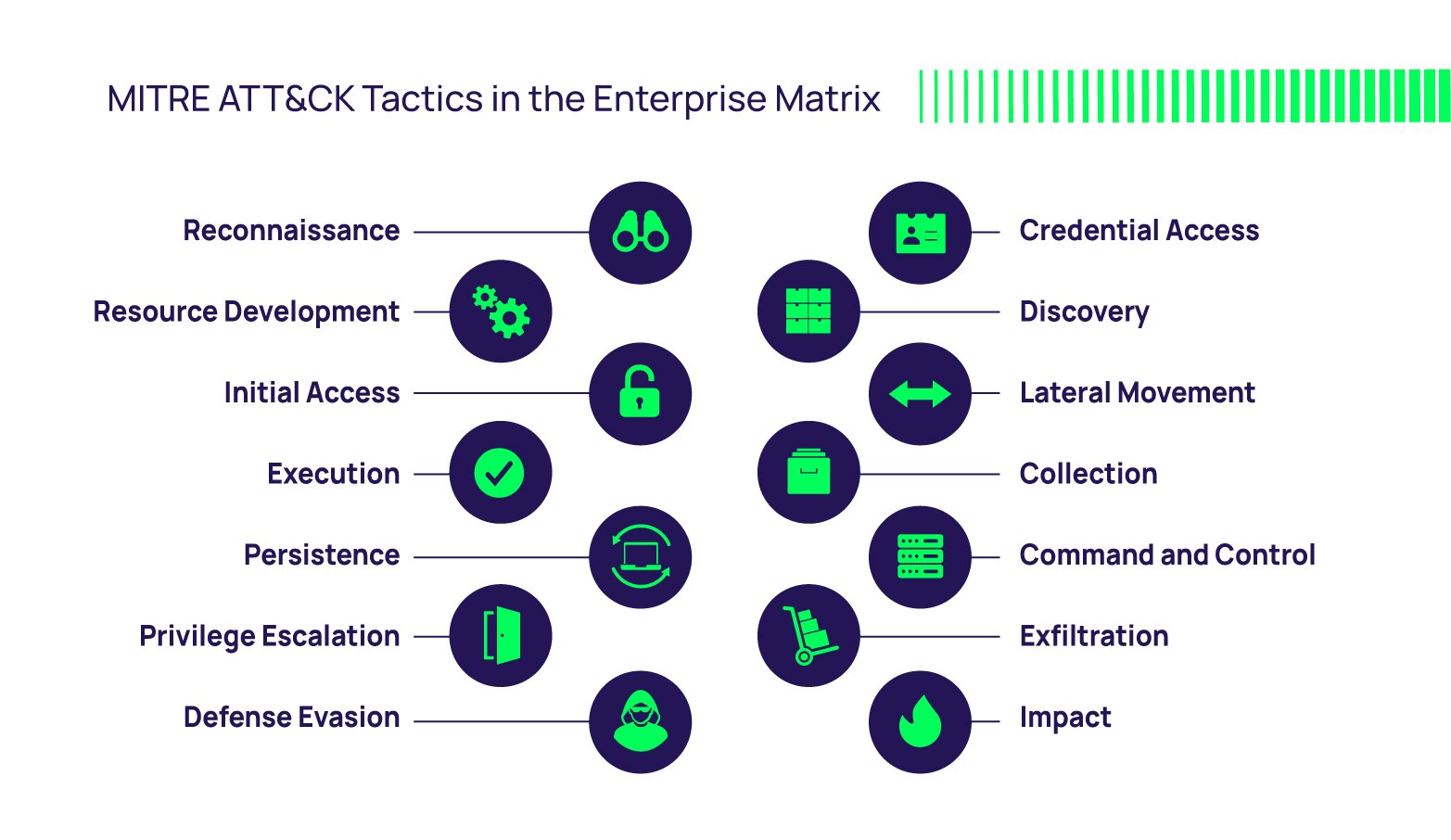
The MITRE ATT&CK Framework
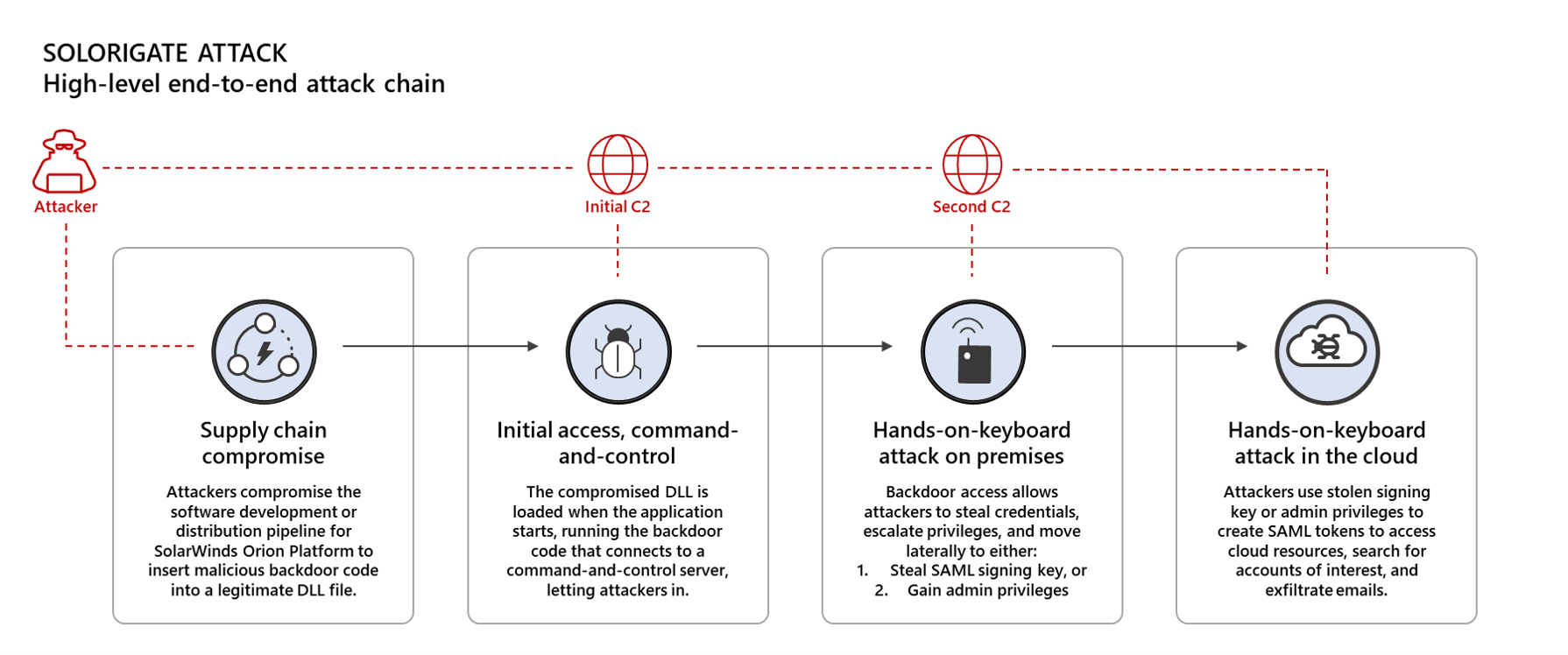
Using Microsoft 365 Defender to protect against Solorigate
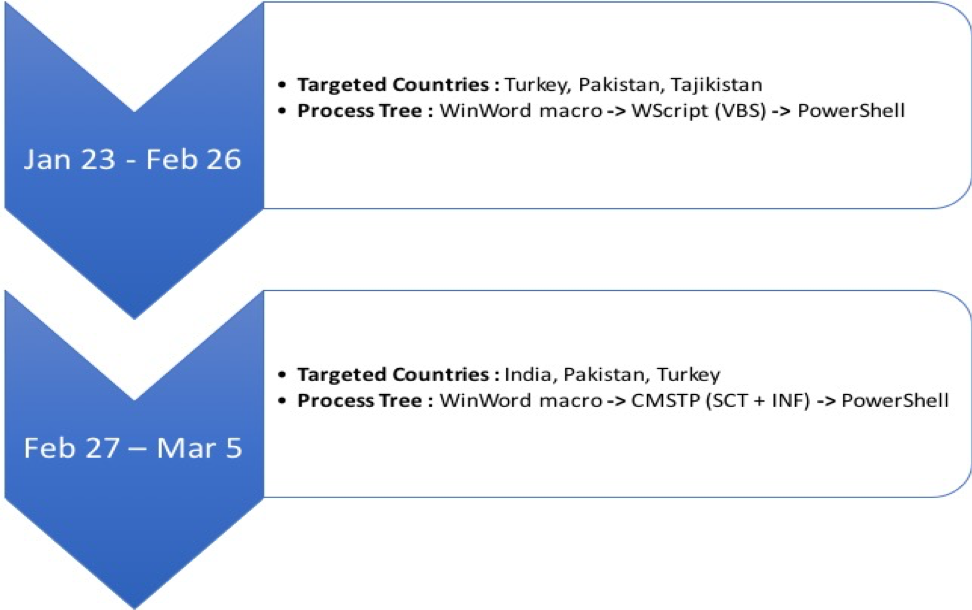
Iranian Threat Group Updates Tactics, Techniques and Procedures in
Inside the Mind of a Cyber Attacker
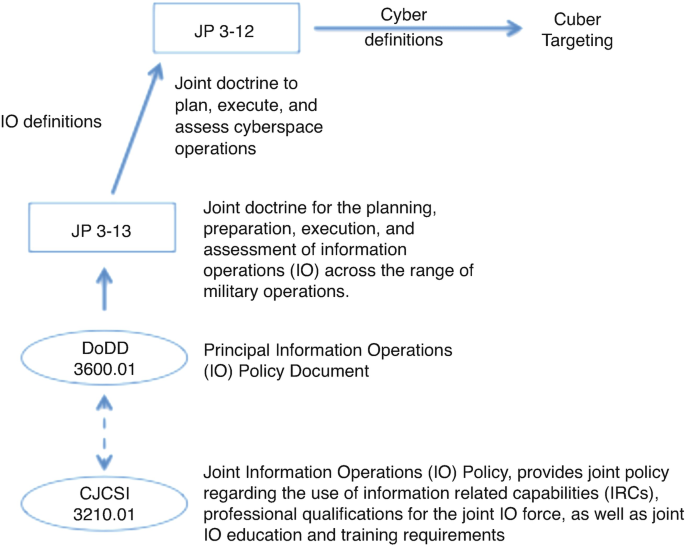
Cyber Policy, Doctrine, and Tactics, Techniques, and Procedures

Cyber Security Firm FireEye Reports Major Breach

Cyber threat attribution using unstructured reports in cyber
Hackers' Favourite Scripting Languages Part 2: Offensive and
de
por adulto (o preço varia de acordo com o tamanho do grupo)