SILKLOADER: How Hackers Evade Detection
Por um escritor misterioso
Descrição
As the cyber threat landscape continues to evolve, hackers are employing increasingly sophisticated techniques to evade detection. One such example is the SILKLOADER malware, which has recently gained attention for its stealth capabilities.

SILKLOADER: How Hackers Evade Detection

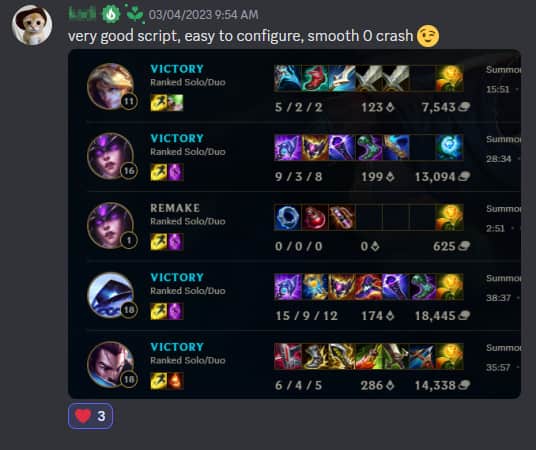
How Hackers Are “Blending In” to Evade Detection
Lynx-CERT

Chinese State-Sponsored Hackers Evade Common Cybersecurity Tools

Exaramel Malware Links Industroyer ICS malware and NotPetya wiper

Malware - Wikipedia

Chinese Hackers Use New Cryptojacking Tactics to Evade Detection

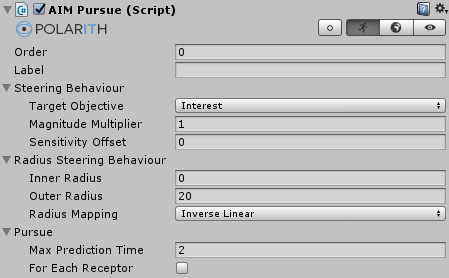
AV/EDR Evasion, Malware Development P-3
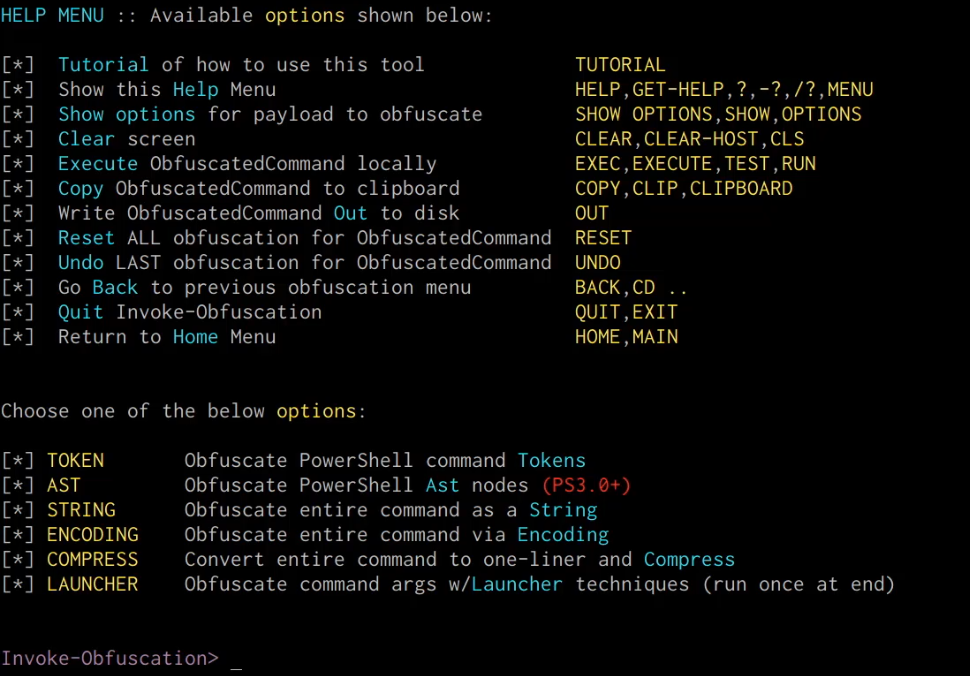
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

SILKLOADER: How Hackers Evade Detection
Risky Biz News: Google wants to reduce lifespan of TLS certificates from one year to just 90 days
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

Chinese hackers use new custom backdoor to evade detection
de
por adulto (o preço varia de acordo com o tamanho do grupo)