Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

MetaDefender Cloud Advanced threat prevention and detection

Malware analysis Program_Install_and_Uninstall Malicious activity

Malware analysis tt.7z Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Dynamic malware analysis [34]

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Complex 'NKAbuse' Malware Uses Blockchain to Hide on Linux, IoT Machines
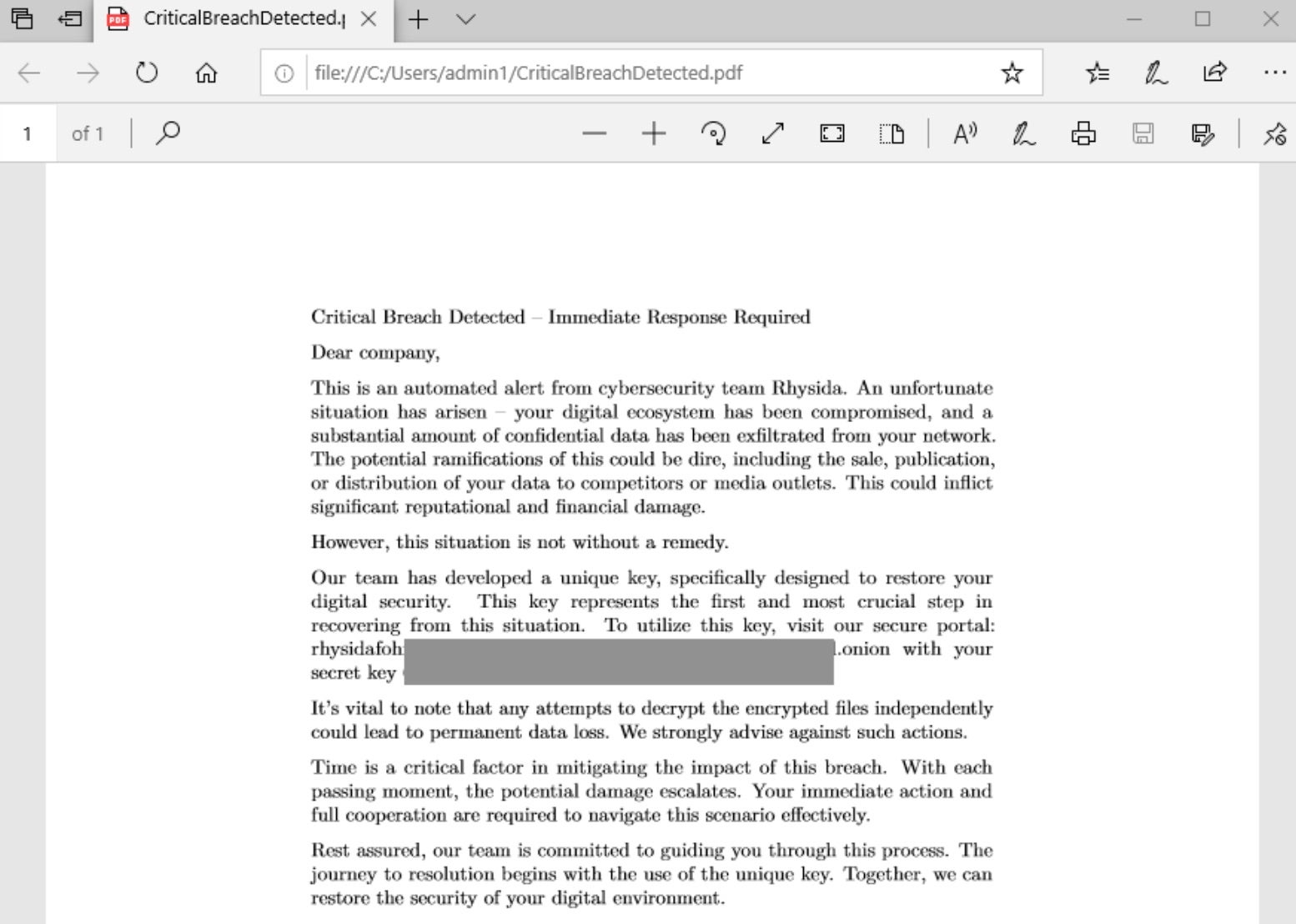
Rhysida - SentinelOne
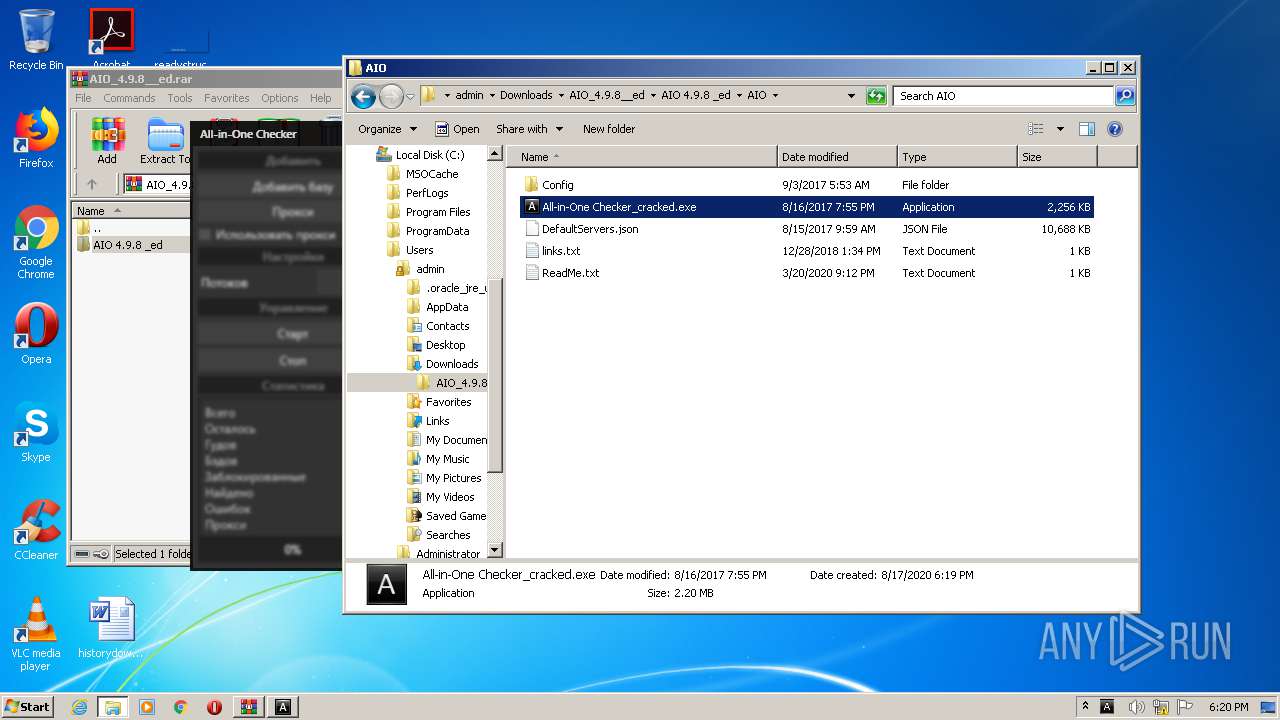
Malware analysis AIO_4.9.8__ed.rar Malicious activity

Remediation and Malware Detection Overview
de
por adulto (o preço varia de acordo com o tamanho do grupo)







